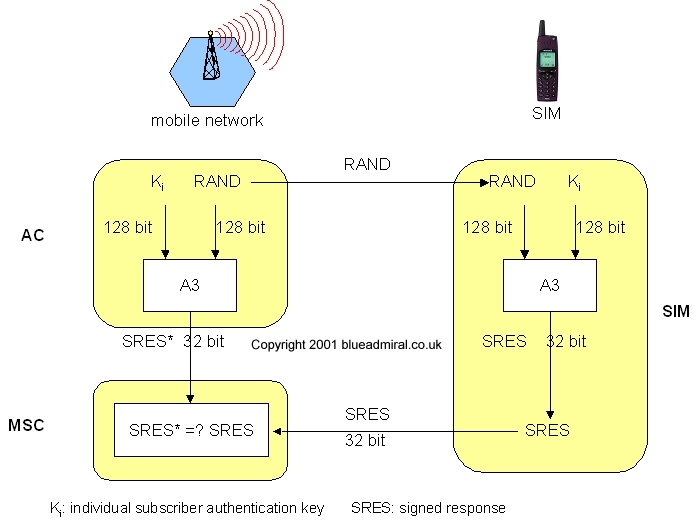
Figure 16 Subscriber Authentication
2.1.7.1 Authentication
As I have already stated before any user can access the GSM system
they must be authenticated as a valid user and this authentication
is done by use of the PIN on the SIM. The SIM stores the users
Individual Authentication Key Ki, the user identification IMSI
and used the A3 algorithm for identification.
The authentication method that is used is challenge - response : the access control will generate a random number RAND as a challenge, and the SIM within the MS has to answer with a signed responses SRES as response. The AuC performs the basic generation of the RAND, signed responses SRES, and cipher key Kc for each IMSI, then forward this information to the HLR, then current VLR then requests the suitable values for the RAND, SRES and the Kc from the HLR.
For authentication the VLR sends
the random value RAND to the SIM. Each side, the GSM network
and the subscriber module, must perform the same operation with
the RAND and the Ki. The MS sends back the SRES generated by
the SIM, the VLR can now compare both values. If the value produced
by the SIM and the VLR match then the user is granted to access
the GSM network, however if they do not match then the subscriber
is refused access to the network. This process is shown in Figure
16
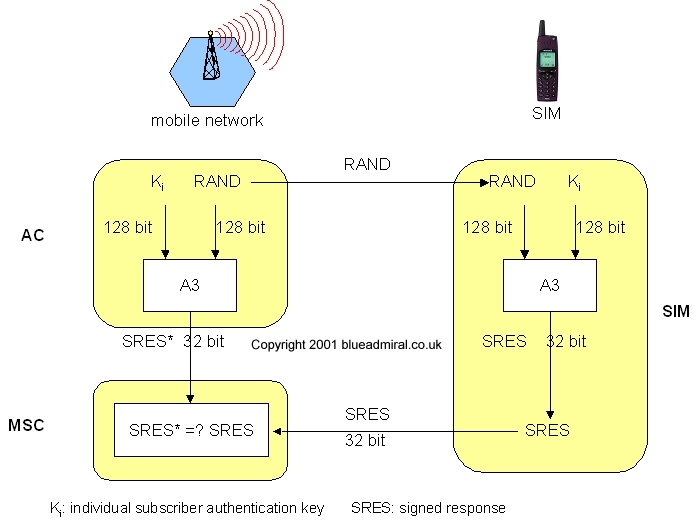
Figure 16 Subscriber Authentication