In the GSM system there is a large amount of user related information transmitted over the air interface and since this is the weakest part of GSM system it uses encryption to ensure privacy. After the user has been authenticated, the MS and the BTS can start using encryption by applying the cipher key Kc. Kc is generated using the individual key Ki and a RAND by applying the A8 algorithm. However it should be noted that that the SIM in the MS and the network both create the same value Kc based on the RAND. The Kc itself is not transmitted over the air interface.
The MS and the BTS can now encrypt and decrypt data using the A5 algorithm and the Kc. You can see the encryption and decryption process in Figure 17, Kc should be a 64 bit key - this however this level of encryption is not very strong, but provides enough protection to stop simple eavesdropping.
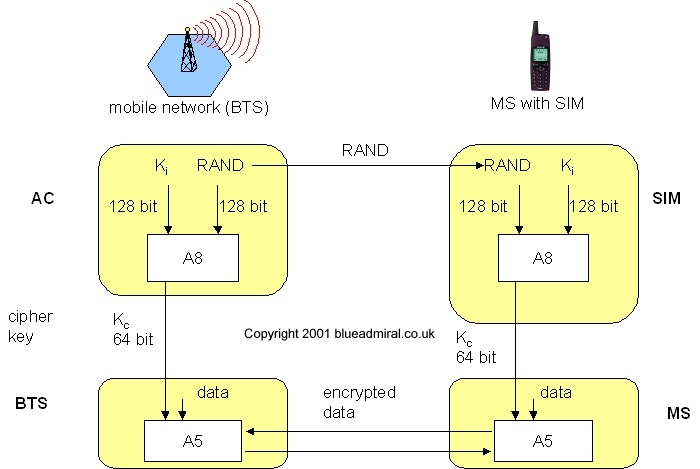
Figure 17 Data Encryption
Since the publication of the algorithm's A3 and A8 on the Internet, it has show that there are certain limitations for example 10 of the 64bits are always set to 0, hence the real length of the key is only 54 bits. The consequence of this is that the encryption is much weaker.